How long should you wait to release an exploit publicly after you notify a company of a flaw in their software? Some organizations like CERT have a 45-day disclosure policy while Google’s Project Zero has a 90-day policy and ZDI has up to 120-days. Balancing the right amount of time can be tricky but a responsible disclosure is vital to ensure you are contributing to the overall security of the internet and not enabling threat actors.
A responsible disclosure’s timeline starts after the identify an exploit and built a proof of concept. Ethical hackers are expected to:
- Notify the software vendor
- Provide the Proof of Concept
- Provide them a reasonable amount of time to patch the software
- Release the exploit publicly
By providing the company time to patch the software, you enable them to push an update to their users before the exploit is released publicly. The knowledge that you will release it publicly is the forcing function for companies to take the exploit seriously and not prioritize their latest feature enhancement over security.
This is a good model for today’s environment – especially when organizations award the ethical hacker with a bug bounty.
What happens when a company fails to take action?
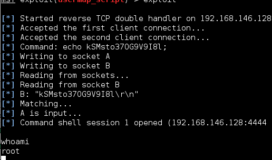
Reportedly, 20-year-old James Lee contacted Microsoft regarding two 0day vulnerabilities he found in both Microsoft Edge and Internet Explorer over 10 months ago. Yet, despite providing a proof of concept detailing the attack, Microsoft failed to take any action to patch the issue.

Both of these vulnerabilities enable a remote attacker to bypass Same Origin Policy which is a security feature designed to block webpages from interacting with each other. This way, if an attacker is able to get a victim to click on a link to his customer webpage the data from the other sites open in the browser are protected.
The now publicly available exploits for the browsers open the doors for hackers to conduct universal cross-site scripting attacks against any victim using either of the browsers until Microsoft releases their patch.

This means that upwards of 15% of desktop users currently using these browsers are vulnerable to this threat and, as reported by the NSA, hackers weaponize known vulnerabilities within 24 hours. It won’t be long before we see these exploits incorporated in phishing campaigns.