Nmap is an essential tool for any recon. This flexible and powerful tool will provide you with all the capability you need to begin any reconnaissance for a pentest or capture the flag exercise. It’s
Host Identification
Nunning Nmap against an IP range will identify open hosts on the network. This can give you your list of targets for a pentest or capture the flag exercise. An example syntax is nmap -sN 10.0.0.200-250 to search through the IP range. Nmap has a number of functions to provide information on the network between you and your target.
- –packet-trace : Nmap scan will display the status and packet summary information.
- –version-trace : Nmap will display each step of its version probe on its output
- –traceroute : Nmap will display routing information between you and the target
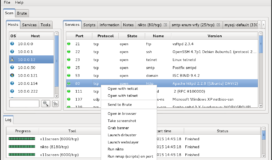
Port Scanning
Nmap’s primary function, running it against any target, or list of targets, will provide you with a list of open ports on the target. There are several built in options that you can utilize to increase the speed or effectiveness of the scan to meet your needs.
- -p : Lets you select the ports you want scanned. You can specify a single port=”-p 53″ a range=”-p 1-1024″ or separate ports=”-p 25,53,445″. This option will be essential to ensuring your scan is appropriate in scope, time, and stealth.
- -F : A fast scan which only checks the 100 most common ports. This is useful if scanning a whole range of targets
- -Pn : The scan will not ping the target system, just scan the ports. This trigger is useful if the target machine or firewall protecting it automatically drop ping packets.
- -sN : No port scan for host identification (previously known as -sP)
- -sS : Indicates a SYN scan, sometimes referred to as a half-open scan or Stealth Scan.
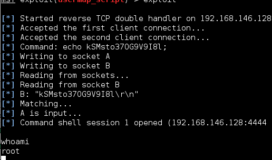
- -sV : This scan will attempt to determine the version of the service running on the open ports. I cannot emphasize enough how vital this can be to exploiting a machine. If you are able to enumerate a service running with a known vulnerability you can find open source information from sites like exploit-db.com on how to gain access to the host.
- -sT : Nmap will use TCP in the scan (default)
- -sU : Nmap will use UDP in the scan (use with sT for Nmap to use both)
- -6 : Nmap will use IPv6

Operating System Fingerprinting
Adding a “-O” or “-O2” to the Nmap scan will cause Nmap to send specifically crafted packets to the targets in attempt to identify which operating system is running on the host. This can be incredibly useful when attempting to determine potential vulnerabilities on the machine.
Output Formats – Nmap can store the output of its scan into several formats. Based on the number of targets, this may be a good way to store the information to use later. The formats are:
- -oN file : stores the output in the normal format typically displayed to the terminal
- -oG file : stores the output in a format with on line per host. This makes the file very easy to grep for (hence the G) if you need to search through it at a later time. This will be very useful for outputs with many hosts.
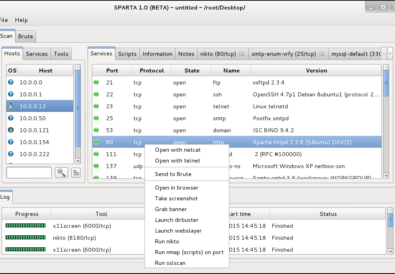
- -oX file : stores output in XML format which is incredibly useful for input into other tool databases like metasploit, zenmap, or sparta.
- -oA file : stores output in all three mediums named file.nmap, file.gnmap, and file.xml
Nmap NSE Scripts
The Nmap Development Team has added several dozen scripts to their framework to automate major portions of the vulnerability scan. If the rules of engagement for your pentest or capture the flag allow you to perform these scans, I highly recommend you take advantage of them.
- To use your scripts against the target simply type –script followed by the script name. For example, say you wanted to run all the default and vulnerability scripts against a target host (10.0.0.4) with smb you would type nmap -p 139,445 –script default,vuln 10.0.0.4. This will provide a massive amount of information on the target from vulnerabilities against it, to operating system information, and possibly password policy. Using default and vuln are personal favorite combination of mine but other categories include: auth, broadcast, brute, discovery, dos, exploit, external, fuzzer, intrusive, malware, safe, and version.
- If you are trying to be a little stealthier and prefer selecting a specific script to run you can search through the NSEscripts you have available on your distro simply type locate nmap/scripts. Narrow down the search by piping your search into a grep. For example, if your host has SMB running and you want to see what scripts are available to run against it, type locate nmap/scripts | grep smb.
- To run several scripts you will need to manipulate arguments with –script-args. Fortunately, if you forget to set them or do not know, Nmap will inform you when you try to run it. An example of this would be nmap –script snmp-sysdescr –script-args snmpcommunity=admin example.com

Nmap is one of the most versatile and useful tools for anyone in this industry. Head over to nmap.org or utilize the man-page to discover additional selectors and scripts that may help meet your specific needs. Thanks to Fyodor and the Nmap Development Team for providing us such an impressive tool.