Credential stuffing is far from a new technique yet people’s propensity to re-use credentials has escalated the number of organizations trying to gain initial access through this vector. The opportunity for credential stuffing occurs when a data breach of user names and passwords is stolen from an organization.
The hacker takes the hashed passwords and cracks them offsite with open source tools like John the Ripper and adds it to a list for automated login attempts. If the victim of the first data breach re-uses the same login and password for the second site, the hacker will be able to quickly login and access the account.

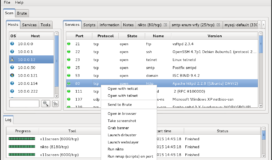
How prevalent are these attacks? Akamai, the content delivery network and cloud service provider, recently reported nearly 30 billion credential stuffing attacks in 2018 alone. Hacking teams are automating the attacks using botnets to disperse the location of the attack. Once they successful validate the account credentials, they are then “sold, traded, or harvested for various types of personal information.”
The media, gaming, and entertainment industries are prized targets for criminals who are looking to trade in stolen information and access. The accounts are sold in bulk, and the goal for the criminals is to move their goods by volume, rather than single account sales
Akamai – State of the Internet / Security Volume 5
So How Do Hackers Get The Credentials?
Data breaches are happening all the time. They are becoming so ubiquitous that they are barely raising headlines or causing people to take notice. One writer compiled all the records leaked in just the month of March, 2019. In total, over 2.1 Billion records were leaked during the 31-day period.
These stolen accounts are quickly cracked and sold on the dark web. Using bitcoin, some criminals are able to compile lists of over 773 million cracked accounts and will sell to other criminal or hostile actors. They will even sell software called All In One (AIO) programs which will automatically target company APIs or login forms to validate the accounts against. This has drastically lowered the bar for entry into this criminal enterprise.
Fortunately, there are some practical defenses organizations can take to defend their users from this type of attack. OWASP lists their top 5 defensive measures as:
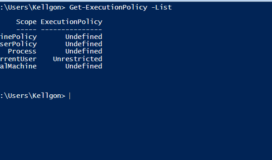
Multi Factor Authentication to mitigate the usefulness of the stolen password. This is the best defense but has the highest costassociated with implementation.- Multi-Step Login Process to defeat most of the automated AIO programs. This will defeat the majority of attackers out there but novel automated programs are designed to defeat these processes over time.
- IP Blacklist to raise the cost of the attack to those who have access to a functional botnet.
- Device Fingerprinting to rule out anomalous login data that doesn’t match standard operating system, geolocation, and language
- Disallow email addresses as user IDs to force users to come up with unique user names.
Whichever methods are used to protect user accounts, it is equally important for the security operations center’s SIEM to have specific rules in place to identify an abnormal quantity of failed logins. Strong oversight is vital to the overall detection and mitigation of cyber attacks.