John the Ripper is one of the most common and powerful password crackers on the market. John has a Pro version which includes some extra useful features but most of the prime functionality a pentester needs can be found in its free version. John is able to take dozens of different password hashes, pilfered from the SAM database or shadow file, and attempt to crack them. There are four different modes you may use to best crack password.

- Incremental – Brute force attack. Try 100% of combinations using characters in either the ASCII, LM_ASCII, Alnum, Alpha, LowerNum, UpperNum, LowerSpace, Lower, Upper, or Digits set of lists.
- Single Crack – Intelligent attack. Use login and GECOS information to mangle wordlists together in an attempt to crack passwords that were made with common user laziness. It will also retry previously successful passwords since most users don’t change their passwords across different accounts or it may have been the default password when accounts were created.
- Wordlist – Dictionary attack. Provide John a wordlist, like rockyou.txt in kali, and it will cycle through until it finds a match. The better the wordlist, the more successful this method is. You can find online wordlists from passwords cracked during major hacks. The millions of used passwords you can expect to be used again more often since we humans are not as creative as we like to think.
- External – Custom attack. Provide John your own guessing code in a configuration file. Usually written in a subset of C.
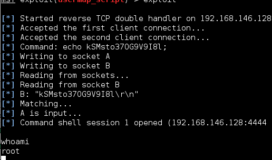
If you run john and it successfully cracks a password it will store it in a file called john.pot which you can view through the “john –show [file]” or “cat john.pot” commands. In this instance, the [file] is the file john ran the attack against, not the john.pot file.

Since password attacks can take an immense amount of time when users implement good password policy, John stores its status in a john.rec file every 10 minutes. In the instance of a crash or pause you can restart where you left off with the “john –restore” command so you don’t lose all the previous computing.

Example: john –wordlist=/usr/share/wordlists/rockyou.txt pass.txt
Show successes with: john –show pass.txt