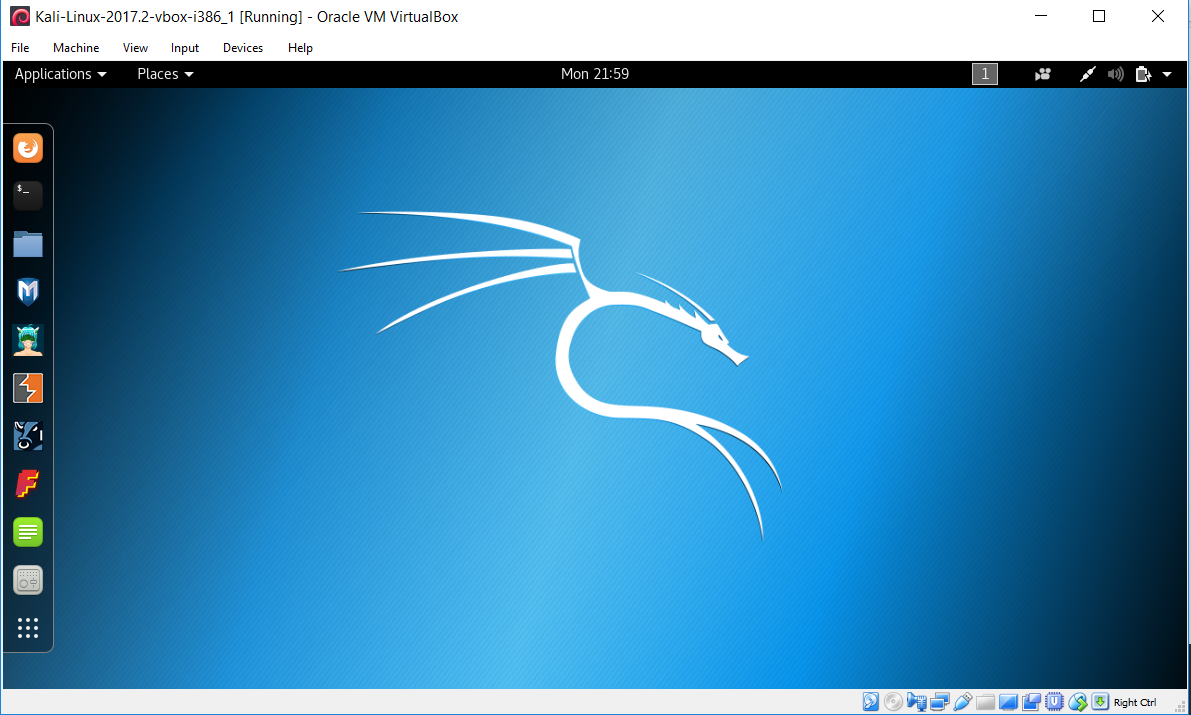
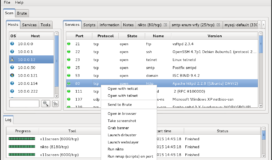
Before you can execute your first exploit you need to get set up with the right environment. For any beginners, Kali Linux is the best place to start. It is an open source Linux distribution that comes complete with the tools necessary to begin advanced penetration testing. To get running with your own Kali environment, simply follow these steps:
1 – First, you want a virtual machine(VM) hypervisor. A virtualized environment is often superior to installing the operating system directly on your machine because you can quickly save, delete, or create new instances as necessary. The two most commonly used are VMware and VirtualBox. Both are more than powerful enough to complete all the operations on this site and the differences fall in price per features and user preference. VMware “player” version and VirtualBox are both free options available to you.
2 – The next piece is getting the operating system to run on your hypervisor. Head over to the Kali download site and get the latest VM for whichever hypervisor you picked. You may also want to consider downloading both the 32 and 64 bit versions of Kali. Certain exploits must be compiled before they can be run on the victim’s machine. It can often be much easier to compile the exploit on a matching x86 vs x64 system rather than using a cross compiler.

3 – Open your new virtual machine by clicking the play button to resume or start the VM and login with the default username of “root” and password “toor”

4 – Open a terminal prompt by clicking on the black box, second from the top in the left panel, and immediately type passwd followed by a new password for your root account.

5 – Run Ping against a known entity like google’s DNS server 8.8.8.8 to check your connectivity. If you are having trouble it could be due to your hypervisor NAT vs. Bridged settings or lacking eth0 in your /etc/network/interfaces.
At this point you have a fully functional Kali distro and all the tools necessary to begin your endeavors in penetration testing. The next step is to learn how to conduct a deliberate recon in order to find potential vulnerabilities in your target.