In an attack now being dubbed ShadowHammer, Taiwan based tech company ASUS was compromised by a hacking team that used its trusted update to push malware down to half a million users throughout the globe. This is the latest software supply chain attack in a growing trend where hackers are gaining initial access to systems by attacking their less-secure elements in the supply chain rather than the system itself.
These attacks are especially notable because gaining access to a multi-billion dollar tech company like ASUS, enables the hacking team to quickly push millions of trojans through an automated update service that will appear entirely as benign and normal behavior on the network. In many cases, the update is even signed by the hacked company, enabling it to bypass most defensive solutions. Historical examples like NotPetya and CCleaner resulted in upwards of 10 Billion dollars of damages.
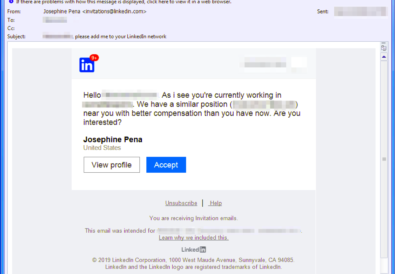
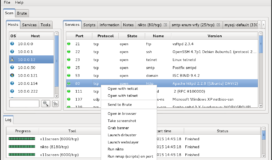
The threat actor modified the ASUS Live Update Utility, which delivers BIOS, UEFI, and software updates to ASUS laptops and
Kaspersky Antivirus Reportdesktops, added a back door to theutility, and then distributed it to users through official channels.
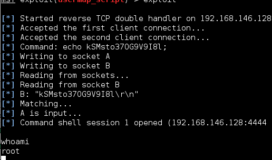
Fortunately, this operation appears to have been a targeted attack against specific systems – likely indicating the authors are part of an Advanced Persistent Threat (APT) team. Once installed, the malware compared the MAC address of the victim to its list of around 600 targeted systems. If the victim’s MAC address matched one on the list, the malware connected to a remote command and control server, asushotfix[.]com, to download and install additional malware for follow-on operations. The domain has since been taken down.
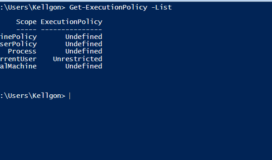
As these attacks grow in popularity, it is time we take a hard look at the vendors we are using to procure both our software and our hardware. These solutions are the building blocks of our IT infrastructure and our implicit trust model that we are using based on their name, location, and validated digital signature only keeps us as secure as the weakest link in that chain.
To address this growing concern, the US Department of Homeland Security (DHS) established an Information and Communications (ICT) Supply Chain Risk Management Task Force back in November of 2018. This task force is a partnership comprised of leading industry companies and government organizations.
Executive Committee members agreed that the Task Force would begin by conducting an ecosystem analysis of existing industry and government supply chain initiatives to identify consensus best practices and concentrate efforts on critical gaps.
Unfortunately, like previous cyber-attacks, companies are unable to rely on their government to fully protect them from outside attacks. This necessitates the need to monitor the software hygiene and cyber risk of all third-parties. In response to this, we are seeing a rise in companies like NormShield, RiskLens, and Deloitte’s CyberGRX who have identified the market problem and begun offering Cyber Risk Scorecards that customers can purchase on potential vendors to help inform their decisions.