Currently Browsing: security
Credential stuffing is far from a new technique yet people’s propensity to re-use credentials has escalated the number of organizations trying to gain initial access through this vector. The opportunity for credential stuffing occurs when a data breach of user names and passwords is stolen from an organization. The hacker takes the hashed passwords and […]
How long should you wait to release an exploit publicly after you notify a company of a flaw in their software? Some organizations like CERT have a 45-day disclosure policy while Google’s Project Zero has a 90-day policy and ZDI has up to 120-days. Balancing the right amount of time can be tricky but a […]
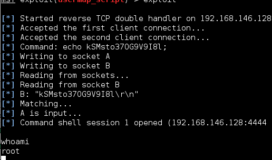
Local File Inclusions occur when an HTTP-GET request has an unsanitized variable input which will allow you to traverse the directory and read files. This attack can often provide key information during a reconnaissance and can sometimes be used to gain remote code execution. A website will indicate it is getting variables with a ? […]
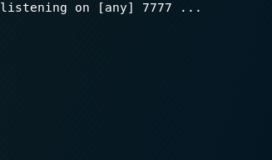
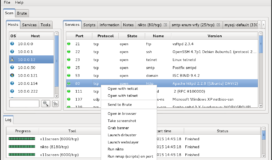
Before you can execute your first exploit you need to get set up with the right environment. For any beginners, Kali Linux is the best place to start. It is an open source Linux distribution that comes complete with the tools necessary to begin advanced penetration testing. To get running with your own Kali environment, […]