Currently Browsing: June 2019
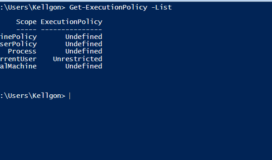
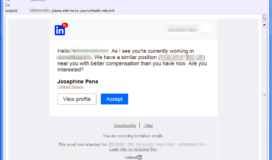
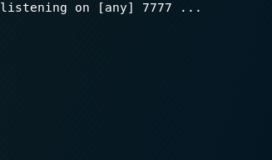
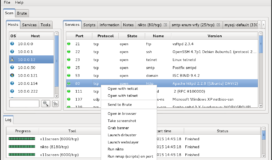
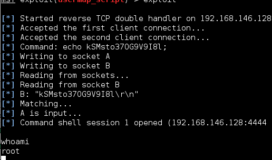
When you initially exploit a system you will usually have a limited shell, especially when conducting client-side exploits. The next step will be upgrading from this shell to a new one with root/system privileges. There are varied methods to accomplishing this escalation which differ highly depending on whether it is a Windows or Linux system. […]